
Cloud Security Best Practices for Businesses in 2025
In today’s digital world, businesses are increasingly relying on cloud computing to store data, run applications, and collaborate with teams. The cloud offers incredible benefits like scalability, cost savings, and flexibility. However, with these advantages come new challenges, especially when it comes to security. As cyber threats become more sophisticated, businesses must prioritize cloud security to protect their sensitive data and maintain customer trust. By 2025, cloud security will be more important than ever. In this blog, we’ll explore the best practices businesses should follow to ensure their cloud environments are secure, compliant, and resilient against cyber threats. Whether you’re a small business or a large enterprise, these tips will help you stay ahead of the curve.

What is Cloud Security, and Why Does It Matter?
Cloud security refers to the measures and technologies used to protect data, applications, and infrastructure in cloud environments. It involves safeguarding your cloud resources from cyberattacks, data breaches, and unauthorized access.
Why is cloud security so important? Here are a few reasons:
Data Protection: Businesses store sensitive information like customer data, financial records, and intellectual property in the cloud. A breach could lead to significant financial and reputational damage.
Compliance: Many industries have strict regulations about how data must be stored and protected. Failing to comply can result in hefty fines.
Business Continuity: Cyberattacks can disrupt operations, leading to downtime and lost revenue. Strong cloud security ensures your business can keep running smoothly.
Customer Trust: Customers expect their data to be handled securely. A breach can erode trust and drive customers away.
Cloud Security Challenges in 2025
As technology evolves, so do the challenges of securing cloud environments. Here are some key challenges businesses will face in 2025:
1. Sophisticated Cyberattacks: Businesses store sensitive information like customer data, financial records, and intellectual property in the cloud. A breach could lead to significant financial and reputational damage.
2. Multi-Cloud Environments: Many businesses use multiple cloud providers, which can create complexity and increase the risk of misconfigurations.
3. Remote Work: With more employees working remotely, securing access to cloud resources has become more challenging.
4. Data Privacy Regulations: Laws like GDPR and CCPA are becoming stricter, requiring businesses to take extra steps to protect user data.
5. Shadow IT: Employees may use unauthorized cloud applications, creating security vulnerabilities.
Cloud Security Best Practices for 2025
To address these challenges, businesses must adopt a proactive approach to cloud security. Here are the best practices to follow:
- Security Features: Look for providers that offer built-in security features like encryption, firewalls, and intrusion detection systems.
- Compliance: Ensure the provider complies with industry standards and regulations relevant to your business.
- Reputation: Choose a provider with a strong track record of security and reliability.
- Encrypt Data at Rest: Ensure all data stored in the cloud is encrypted.
- Encrypt Data in Transit: Use secure protocols like HTTPS and TLS to encrypt data as it moves between your devices and the cloud.
- Manage Encryption Keys: Store encryption keys securely and rotate them regularly.
- Multi-Factor Authentication (MFA): Require users to verify their identity using multiple methods, such as a password and a fingerprint scan.
- Role-Based Access Control (RBAC): Assign permissions based on user roles to limit access to sensitive data.
- Monitor User Activity: Use tools to track who is accessing your cloud resources and what they’re doing.
- Automate Updates: Enable automatic updates for your cloud applications and operating systems.
- Patch Management: Regularly apply patches to fix security vulnerabilities.
- Monitor for Vulnerabilities: Use tools to scan your cloud environment for weaknesses.
- Follow the 3-2-1 Rule: Keep three copies of your data (one primary and two backups), store them on two different types of media, and keep one copy offsite.
- Test Your Backups: Regularly test your backups to ensure they can be restored.
- Use Cloud Backup Services: Many CSPs offer backup solutions that automate the process.
- Use Security Information and Event Management (SIEM) Tools: These tools collect and analyze data from your cloud environment to detect suspicious activity.
- Set Up Alerts: Configure alerts for unusual activity, such as multiple failed login attempts or large data transfers.
- Conduct Regular Audits: Review your cloud environment for misconfigurations and vulnerabilities.
- Phishing Awareness: Teach employees how to recognize and avoid phishing attacks.
- Password Hygiene: Encourage the use of strong, unique passwords and regular password changes.
- Data Handling: Train employees on how to handle sensitive data securely.
- Phishing Awareness: Teach employees how to recognize and avoid phishing attacks.
- Password Hygiene: Encourage the use of strong, unique passwords and regular password changes.
- Data Handling: Train employees on how to handle sensitive data securely.
- Use Authentication: Require authentication for API access.
- Monitor API Activity: Track API usage to detect anomalies.
- Limit Permissions: Restrict what APIs can do to minimize risks.
- Create a Plan: Develop a step-by-step plan for responding to security incidents.
- Assign Roles: Designate team members to handle specific tasks during an incident.
- Conduct Drills: Regularly test your plan to ensure it works.
- Following Industry News: Keep up with the latest trends and threats in cloud security.
- Participating in Training: Attend webinars, workshops, and conferences to learn about new security tools and techniques.
- Collaborating with Experts: Work with cybersecurity professionals to assess and improve your cloud security.


The Future of Cloud Security in 2025
As we look ahead to 2025, cloud security will continue to evolve. Here are some trends to watch:
AI-Powered Security: AI will play a bigger role in detecting and responding to threats in real-time.
Zero Trust Architecture: This approach assumes that no user or device can be trusted by default, requiring continuous verification.
Quantum Computing: While still in its early stages, quantum computing could revolutionize encryption and cybersecurity.
Increased Automation: More businesses will automate their security processes to reduce human error and improve efficiency.
Conclusion: Secure Your Cloud, Secure Your Future
Cloud security is no longer optional—it’s a necessity. By 2025, businesses that fail to prioritize cloud security will be at greater risk of cyberattacks, data breaches, and regulatory penalties. By following the best practices outlined in this blog, you can protect your cloud environment, safeguard your data, and ensure your business remains resilient in the face of evolving threats.
At Cybs Innovations, we specialize in helping businesses secure their cloud environments. Whether you’re just starting your cloud journey or looking to enhance your existing security measures, we’re here to help. Don’t wait until it’s too late—start strengthening your cloud security today.
Related Posts
Vexron: The Kill Switch for Unplanned Downtime
Learn how Vexron uses AI and IoT to prevent failure, reduce downtime, and save costs in smart manufa...

From Concept to Cloud: Mastery in IoT Engineering
Discover the full lifecycle of product engineering. From PCB design and embedded firmware to cloud i...
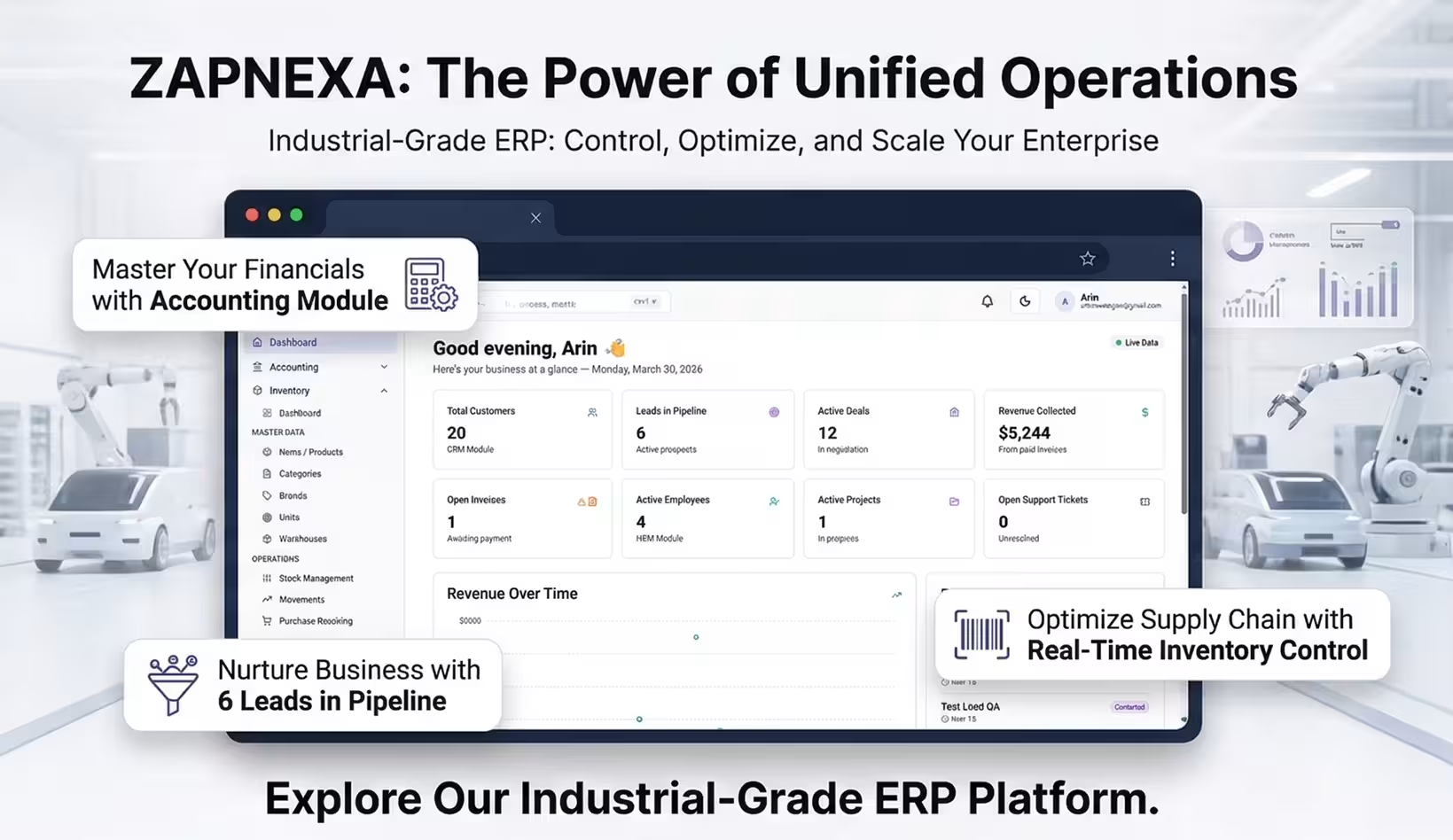
Why ZapNexa is the Future of Business Management
Discover how ZapNexa unifies business operations, enhances scalability, and drives efficiency for ma...

